Global attacks using password lists are on the rise. These attacks are leading to a growing sophistication of typical brute force password cracking attempts using dictionary attack lists. Ensuring you have the correct security measures in place can prevent the loss of sensitive data.
What is a password list attack?
With password list attacks, attackers try to gain access illegally via the regular route with the correct list of passwords and IDs which they have gotten from somewhere previous to the attack. In this case, the login attempt number by the ID becomes so few that it is often difficult to differentiate proper access from an attack.
If the users reuse a common password on multiple sites, there is a real danger of that password being taken, and then used to successfully gain access to other sites. It is for this reason that we recommend that you use different ID and password combinations on each site.
Moreover, the time has come to consider more security measures like 2-step verification on web application servers as well as other methods of authentication.
From the viewpoint of attackers, dictionary attacks, where the attacker attempts to gain access through a variety of common words and passwords which are perceived to be used often, are more efficient than a brute force attack where they just try passwords randomly using as many different possible combinations as they can. Further still, a list of correct IDs and passwords, with the ease at which it allows access, is like a magic item.
It’s also thought that the lists used in dictionary attacks are generally based on reference to publicly available information.
On the contrary, if we refer to a password list beforehand and prevent users from setting a frequently used password, it should be a good system to protect from these types of attacks.
Famous Password List Providing Service
Here, we’ll introduce a renowned list providing service.
■OpenWall
– provides a list for general password tracking which attackers use
– Provides the list on both paid and free services.
https://www.openwall.com/wordlists/
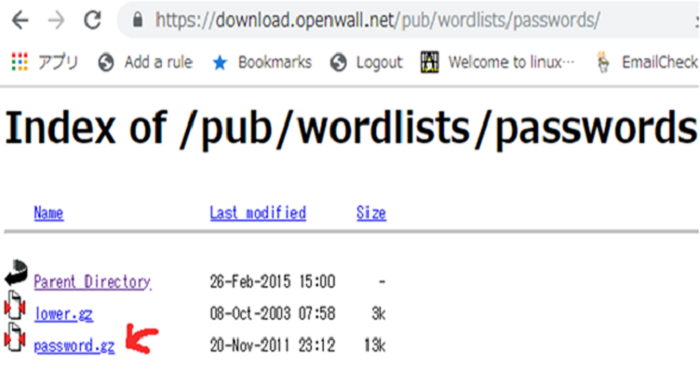
I tried to download the list in the free version.
https://download.openwall.net/pub/wordlists/passwords/
When you unzip the password.gz, you will see a file called” password.lst.” Open it with the. list viewer. It shows “Last update: 2011/11/20 (3546 entries) “. It seems that they have not updated the free version for a long time. The possible passwords are listed in order of appearance, but I was a little surprised that this included the password I usually use.
What also surprised me was just how common some of these passphrases are, similar permutations of the same word or phrase appear through the wordlist and the dictionary file shows that users feel changing a password to lowercase makes it more difficult to crack.
Here is a list of the top 20 most used passwords:
| 1 | 123456 | 11 | 1234 | 21 | service |
| 2 | 12345 | 12 | qwerty | 22 | canada |
| 3 | password | 13 | money | 23 | hello |
| 4 | password1 | 14 | carmen | ||
| 5 | 123456789 | 15 | mickey | ||
| 6 | 12345678 | 16 | secret | ||
| 7 | 1234567890 | 17 | summer | ||
| 8 | abc123 | 18 | internet | ||
| 9 | computer | 19 | a1b2c3 | ||
| 10 | tigger | 20 | 123 |
As you can see all of the phrases on the list are English words with very little use of special characters, nor many complex passwords included. Moreover, the attackers use a list of words such as the one above by inputting it into a tool such as John the Ripper, THC-Hydra or Medusa. We won’t explain the details on the usage of these tools here. In any case, If attackers use these tools and you can detect the access from them, you can defend against their attacks.
We recommend using cloud bot attack detection to detect any usage of the above tools and defend yourself from any potential attack in the future.
How to Protect Against Brute Force Dictionary Attack Lists
CDNetworks offers the cloud bot attack countermeasure “Bot Shield,” which is able to detect and defend recently increasing cyber-attacks.
Bot Shield is a cloud bot countermeasure integrated with the global CDN platform. It is equipped with multiple features that detect and block increasing cyber-attacks via bots beforehand, strengthen web security, and provide high-performance and highly-available web delivery.
It also helps to detect unknown attacks (zero-day) by bots, protects your website from a wide variety of attacks, including those using the dictionary attack list method.