It’s pretty remarkable how much the use and advancement of the cloud has changed the way enterprises – and their employees – operate. From enabling globetrotting salesmen to log in to company databases to accessing documents on a smartphone, cloud computing has transformed IT and the possibilities continue to grow. With the benefits on offer it can be easy to believe that no drawbacks exist but when it comes to the cloud security remains a crucial consideration.
While opportunities abound with cloud resources, there are challenges and pitfalls, as well as different methods to achieve your desired results. Should businesses go with a public cloud service, or opt for a private cloud housed on company property? Is the best option a hybrid mixture of public and private cloud use? In this guide, we consider both public cloud security and private cloud security to evaluate the pros and cons of both.
What is the Difference Between Private and Public Cloud Security?
Private cloud security refers to the protection of data and applications that are stored in a dedicated cloud environment that is isolated from other organizations. This isolation provides a higher level of security as compared to a public cloud environment.
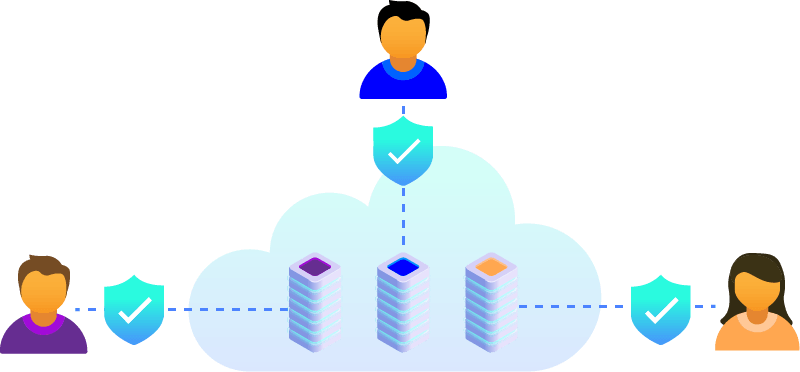
Public cloud security, on the other hand, refers to the security measures put in place to protect public cloud environments that are accessed by multiple users or organizations. In a public cloud environment, users must rely on cloud providers to implement security measures to ensure the protection of their data.
While private cloud environments offer increased security through isolation and a dedicated infrastructure, they can also require more resources and expertise to maintain. In contrast, public cloud environments typically offer a range of security tools and services, but their shared infrastructure can create certain risks such as data breaches.
In any cloud environment, a range of security measures such as data encryption, access controls, and regular security audits are recommended. Ultimately, the choice between private and public cloud security should be based on an organization’s specific needs and risk tolerance.
Both Private & Public Cloud Services are Expanding
All types of cloud services are on the rise. Data shows the use of public cloud platforms is increasing, but private clouds still carry the majority of workloads.
One of the reasons public cloud environments are growing in popularity is that it requires no capital investment on behalf of the user. With a public cloud, businesses purchase server space from a third-party provider, eliminating the need for physical servers, storage systems, and other related on-premise IT costs.
The servers are multi-tenant cloud deployments, meaning other companies’ data may be stored on the same server as your company’s data. Many businesses use some form of public cloud application, whether it’s for email (i.e. Gmail), sharing documents (i.e. DropBox), or hosting web servers.
Private clouds, on the other hand, are single-tenant solutions. This is where a company owns and operates the servers, or leases dedicated servers from a datacenter. A private cloud’s hardware can be stored on-site at a company’s property, or housed in a datacenter. In strictly regulated industries, such as finance and healthcare, a private cloud is a regulatory requirement.
Determining and implementing the best cloud solution for your business is not an easy matter. There are three main points of difference between the public and private cloud: access, network security, and continuity. Let’s take a look.
How Effective is Cloud Security
There’s been quite a bit written about cloud security and there’s a good reason for it. Security in the cloud – whether in a public or private cloud scenario – is a business necessity. Cloud adoption is continuing at a rapid pace and for good reason.
However, depending on the industry and type of information stored in a public cloud, there may not be enough privacy and security policies in place. These shortfalls contribute to public cloud environments increasing the attack surface for potential hackers, particularly with the use of sophisticated malware. Data loss is a huge concern here as those using this service have little control over any vulnerabilities that may materialise.
A private cloud offers the most control over cloud security challenges because all security efforts are done in-house, or are outsourced to a managed security provider. In addition to that, the security tools available with a private cloud include greater levels of authentication, API-enabled protection , additional layers of automation, and the potential for scalability if required. All of which contribute to a greater level of data protection.
There are options for businesses looking for an increased security posture while taking advantage of flexible public cloud infrastructure, such as a cloud-based content delivery network. At CDNetworks, our cloud security solutions provide DDoS protection, security for web applications and websites, and allow for the secure transfer of information over the internet.
Our cloud-based global infrastructure also accelerates real-time content delivery to your customers around the world, reducing security risks.
Access Control to Cloud Infrastructure
One of the greatest advantages of the cloud is it makes organizational data accessible with an internet connection. That’s the end result but, as IT professionals know, there are many steps and considerations to get to that endpoint successfully.
In a traditional data storage model, companies would have a locked dedicated server room on-premises that was monitored and maintained by IT staff and if needed, security teams. To access data stored on the servers, employees would have to log in from a network computer.
When storing company data and communications, the question of who has access to that vital information has always been a concern.
With a public cloud, the IT staff will likely never see the physical servers that house the company’s data. In most cases, it’s difficult to know who will have access to your servers (and the data that’s on those servers) at the datacenter.
In the public cloud model, companies pay for space and for what they use, and your company’s data could be stored on the same server as other companies. Firewalls and other cybersecurity measures are sometimes managed by the cloud service provider as well, which frees up IT staff from day to day management, but also leaves your company’s data at risk of a data breach if there’s a lapse in security procedures on the public cloud providers end or unidentified misconfigurations.
However, most companies offering cloud based security services implement what is known as Role-Based Access Control and Authorization (RBAC) into the network. This is an important security measure used to limit access to systems or networks. It defines roles which group together users with similar access rights and privileges. Only administrators can configure the rights and privileges of each role, which helps to prevent unauthorized access and misuse of the system.
Access can be further restricted with a private cloud solution. A company’s physical servers may be housed in a data center, but the IT department is typically responsible for carrying out data security configurations and monitoring. Physical protections, such as a locked cage for your company’s servers, can also be implemented depending on the security controls in place.
Continuity
As more and more mission-critical applications, services, and sensitive data is stored in the cloud, it becomes increasingly important to ensure your cloud solution is available 24/7.
Both public and private clouds promise always-on solutions, but what about remediation in the event of a disaster or cyber attack? Does the cloud solution have a plan in place? Does your cloud solution have built-in redundancy or the ability to absorb large amounts of traffic in a DDoS attack?
Public clouds often have a large capacity when it comes to security measures which will most likely involve multi-factor authentication as well as physical security for gaining access to any areas containing sensitive data, firewalls for the protection of network security, and an extensive auditing program to ensure the continual monitoring of such systems.
But the ability to expand on-demand largely depends on the service provider. Depending on the configuration and available space on private clouds, a disaster could put key business solutions and security services offline.
Private clouds have the ability to spread the workload over multiple servers but are limited by the amount of server space a company owns or operated.
A hybrid cloud solution – one that involves public and private clouds – could help diversify data storage, protecting assets in the event of a disaster or attack.
Pairing your company’s cloud with a CDN provides access to a global network of cloud-based technologies. CDNetworks has more than 2,800 points of presence (PoPs) across the world. If there is a natural disaster in one area of the world, there are other servers ready and waiting to pick up the traffic ensuring continuity of your website or web-based applications. A CDN can absorb excessive amounts of traffic – a sign of a DDoS attack – and our cloud security monitors this activity and alerts customers of the issue.
Final Thoughts on Private and Public Cloud Security
The cloud – public, private, and hybrid cloud environments – are here to stay. Making it work for your business is an ongoing challenge.
Choose your cloud business partners with care; your business will depend on the availability of your cloud, whether it’s key data or an application. The right solution for your business may not come from a single cloud provider and it will likely involve a network of partners across multi-cloud environments.
The very nature of the cloud is its ability to integrate with all areas of your business and a cloud solution reflects that. Security, performance, and availability are all areas to thoroughly consider in your cloud solution.