パスワード リストを使用したグローバルな攻撃が増加しています。これらの攻撃は、辞書攻撃リストを使用した典型的なブルート フォース パスワード クラッキングの試みの巧妙化につながっています。適切なセキュリティ対策を講じることで、機密データの損失を防ぐことができます。
パスワードリスト攻撃とは何ですか?
パスワードリスト攻撃では、攻撃者は、攻撃前にどこかから取得したパスワードと ID の正しいリストを使用して、通常のルートを介して不正にアクセスしようとします。この場合、ID によるログイン試行回数が少なくなり、正当なアクセスと攻撃の区別がつかない場合が多くなります。
ユーザーが複数のサイトで共通のパスワードを再利用すると、そのパスワードが盗まれ、他のサイトへのアクセスに成功する危険性があります。このため、サイトごとに異なる ID とパスワードの組み合わせを使用することをお勧めします。
さらに、Web アプリケーション サーバーでの 2 段階認証やその他の認証方法など、より多くのセキュリティ対策を検討する時期が来ています。
攻撃者の観点からは、攻撃者が頻繁に使用されると認識されているさまざまな一般的な単語とパスワードを使用してアクセスしようとする辞書攻撃は、パスワードをランダムにできるだけ多く使用して試行するブルート フォース攻撃よりも効率的です。可能な限り可能な組み合わせ。さらに、正しい ID とパスワードのリストは、簡単にアクセスできる魔法のアイテムのようなものです。
また、辞書攻撃で使用されるリストは一般に、公開されている情報への参照に基づいていると考えられています。
逆に、事前にパスワード一覧を参照し、よく使うパスワードをユーザーが設定できないようにすれば、この種の攻撃から身を守る良いシステムになるはずです。
有名パスワード一覧提供サービス
ここでは、有名なリスト提供サービスを紹介します。
■オープンウォール
– 攻撃者が使用する一般的なパスワード追跡のリストを提供します
– 有料サービスと無料サービスの両方のリストを提供します。
https://www.openwall.com/wordlists/
無料版でリストをダウンロードしてみました。
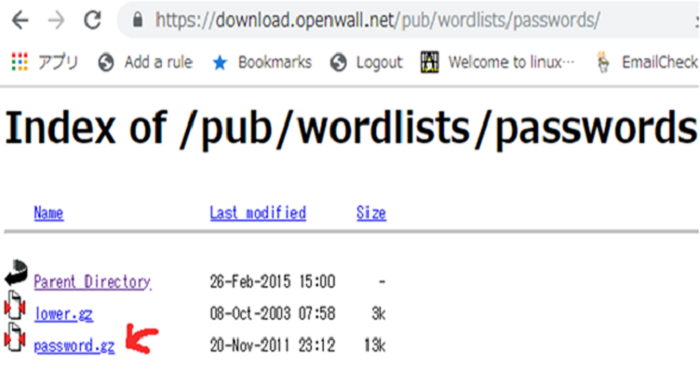
https://download.openwall.net/pub/wordlists/passwords/
password.gz を解凍すると、「password.lst」というファイルが表示されます。で開きます。リストビューア。 「最終更新日: 2011/11/20 (3546 エントリ)」と表示されます。長い間無料版を更新していないようです。考えられるパスワードを登場順に並べているのですが、普段使っているパスワードがこれに含まれていることに少し驚きました。
また、私が驚いたのは、これらのパスフレーズのいくつかがどれほど一般的であるか、同じ単語またはフレーズの同様の順列が単語リストに表示され、辞書ファイルは、ユーザーがパスワードを小文字に変更すると解読がより困難になると感じていることを示しています.
以下は、最も使用されている上位 20 個のパスワードのリストです。
| 1 | 123456 | 11 | 1234 | 21 | サービス |
| 2 | 12345 | 12 | クォーター | 22 | カナダ |
| 3 | パスワード | 13 | お金 | 23 | こんにちは |
| 4 | パスワード1 | 14 | カルメン | ||
| 5 | 123456789 | 15 | ミッキー | ||
| 6 | 12345678 | 16 | ひみつ | ||
| 7 | 1234567890 | 17 | 夏 | ||
| 8 | abc123 | 18 | インターネット | ||
| 9 | コンピューター | 19 | a1b2c3 | ||
| 10 | ティガー | 20 | 123 |
ご覧のとおり、リストにあるフレーズはすべて英単語で、特殊文字はほとんど使用されておらず、複雑なパスワードも多く含まれていません。さらに、攻撃者は上記のような単語のリストを John the Ripper、THC-Hydra、Medusa などのツールに入力して使用します。ここでは、これらのツールの使用方法の詳細については説明しません。いずれにせよ、攻撃者がこれらのツールを使用し、それらからのアクセスを検出できれば、攻撃を防御できます。
クラウド ボット攻撃検出を使用して、上記のツールの使用を検出し、将来の潜在的な攻撃から身を守ることをお勧めします。
ブルート フォース ディクショナリ攻撃リストから保護する方法
CDNetworksは、クラウドボット攻撃対策を提供します」Bot Shield
(Bot対策)」は、近年増加するサイバー攻撃を検知して防御することができます。
Bot Shield は、グローバルに統合されたクラウド ボット対策です。 CDN プラットフォーム.増加するボットによるサイバー攻撃を未然に検知・遮断し、Webセキュリティを強化し、高性能・高可用性のWeb配信を実現する複数の機能を搭載しています。
また、ボットによる未知の攻撃 (ゼロデイ) を検出し、辞書攻撃リスト方式を含むさまざまな攻撃から Web サイトを保護します。