Flood Shield 2.0
A Distributed Cloud-based DDoS Mitigation Solution with WAAP-Ready Protection
Flood Shield 2.0 is a comprehensive cloud-based distributed denial of service (DDoS) protection service that now includes WAAP-ready protection. It delivers a fast, simple, and effective threat-centric DDoS protection that ensures the stability of your origin server, reduces business impact, and improves resiliency against even sophisticated DDoS attacks—including SYN, ACK, UDP, and HTTP Flood attacks—in real-time to ensure you can stay connected and maintain business continuity, even in the face of an attack.
Additionally, Flood Shield 2.0 offers a comprehensive, one-stop experience with a full range of features. It protects web applications, non-web applications, and APIs using adaptive and applicable measures, while providing superior acceleration services. This synergy ensures unparalleled performance, reliability, and unlimited scalability for online services and infrastructures.
Flood Shield 2.0 is deployed on CDNetworks’ global infrastructure, with data centers in the USA, Europe, Asia, and mainland China. With over 40 global DDoS scrubbing centers and 20Tbps of total capacity, Flood Shield 2.0 is ideally suited for protecting websites, web apps, and network infrastructures on large-scale online platforms against all known types of DDoS attacks, regardless of complexity and scale.
- Brochure
- Video
- Blog
- Learn More
Resources
CDNetworks State of WAAP Report 2024
Features
Huge Mitigation Capacity
20+ Tbps of Networks Capacity
40+ Global DDoS Scrubbing Center
Analysis and Logs
Based on dedicated resources, Flood Shield 2.0 provides both L3/4 and L7 analysis and logs
Layered Protection
Integrated layered defense modules, including various customized policies and Web Apps & API Protection, to disrupt cyberthreats in real time and prevent exploitation of your platform
Adaptive Protection
With the help of AI Center Engine, Flood Shield 2.0 learns your business and realizes managed, layered, and adaptive protection with easy deployment.
Integrated Security & Acceleration
Flood Shield offers CDN acceleration services that include smart routing, scheduling, load balancing, and caching.
Full Scenario Adaption
Protocols like HTTP/S, WebSocket, TCP/UDP (applications or ports) are supported to accommodate wide-ranging requirements of your platform’s implementation.
One-stop Web Application & API Protection
Flood Shield 2.0 provides a comprehensive multi-layered security solution that covers DDoS protection, Web Application Firewall (WAF), API security and gateway, Bot management, and specific attack deflection modules to respond to and recover from cybersecurity incidents. By using our single portal for multiple products, you can secure your service and applications while saving significantly on maintenance costs and simplifying operations throughout your entire digital and physical ecosystem.
Cloaked Origin IP
We help increase server security by completely cloaking your origin server’s real IP address. As a result, attackers are unable to identify your origin’s IP address to directly attack your origin server. In addition, we provide you with the IP addresses of our global Points of Presence (PoPs) that you can add to your whitelist to block unnecessary requests, further increasing your security posture.
Big Data Analysis & Machine Learning
With an average of over 3 billion real attack samples collected daily by its threat intelligence library, CDNetworks’ Flood Shield 2.0 is backed by an advanced AI Center Engine, where big data and machine learning capabilities work in concert to enable intelligence processing and analysis mechanisms tailored to scenario-based protection. This setup allows enterprises to better detect network attack trends in real-time and automatically activate defenses in advance, helping them achieve adaptive protection capabilities that strengthen continuously over time.
Seamless Market Penetration Capabilities
By leveraging a robust network of resources and long-term partnerships with local ISP providers in regions boasting large numbers of active digital users such as East Asia, Southeast Asia, the Middle East, and Latin America, CDNetworks offers unparalleled advantages for achieving global reach. Additionally, Flood Shield 2.0 platform utilizes a diverse array of tools and technologies, including dedicated lines, intelligent IP scheduling, link encryption, and hijacking monitoring, to provide tailored network solutions for enterprises entering different regional markets. This approach ensures that users across various locations can access online business platforms effortlessly and deliver genuine benefits to their enterprise customers.
Flexible Pricing
Flexible pricing models provide cost-effective models to meet differing usage models that organizations may have for their risk profiles. This approach allows you to pay in the most effective way that suits your business needs while optimizing cash flow through an OpEx approach. There are unlimited mitigation and elastic mitigation plans that you can choose based on your budget.
Unified Visibility
Flood Shield provides comprehensive visibility into all your DDoS attacks, cyber-attacks, and threats through intuitive security dashboards. These dashboards provide summaries of both Layer 3/4 and Layer 7 attacks, presenting key information such as DDoS attack bandwidth, attack IP lists, attack maps, attack types, and counts. The data is updated automatically in near real-time during attacks to provide up-to-date insights into the threat landscape and help you develop effective strategies to optimize your network security rapidly and combat future threats.
Our Global Scrubbing Center Network
- 200,000+
- Global Servers
- 2,800+
- Global CDN PoPs
- 200+ Tbps
- CDN Capacity
- 20+ Tbps
- Scrubbing Capacity
- 70+
- Countries & Regions
- 40+
- Scrubbing Centers
- 1000+ PB
- Storage Capacity
Scrubbing Center Locations
- Hong Kong, China
- Taiwan, China
- Mainland China (*60 Centers)
- Tokyo, Japan (*2 Centers)
- Surabaya, Indonesia
- Jakarta, Indonesia
- Manila, Philippines (*2 Centers)
- Singapore (*3 Centers)
- Bangkok, Thailand (*4 Centers)
- Ho Chi Minh City, Vietnam (*2 Centers)
- Hanoi, Vietnam
- Karachi, Pakistan
- Mumbai, India (*2 Centers)
- Fujairah, UAE
- Riyadh, Saudi Arabia
- Istanbul, Turkey
- London, England
- Milan, Italy
- Paris, France
- Frankfurt, Germany
- Amsterdam, Netherland
- Moscow, Russia
- Montreal, Canada
- Los Angeles, USA
- New York, USA
- Dallas, USA
- Seattle, USA
- Queretaro, Mexico
- Rio de Janeiro, Brazil
- Sao Paulo, Brazil
- Lima Metropolitan, Peru
How our DDoS Protection Services Work
Flood Shield 2.0 is deployed on CDNetworks’ distributed PoPs. It is a cloud-based “always-on” mitigation service with virtually unlimited capacity. Best of all, it provides transparent scaling automation without requiring sophisticated deployments and changes to customer networks.
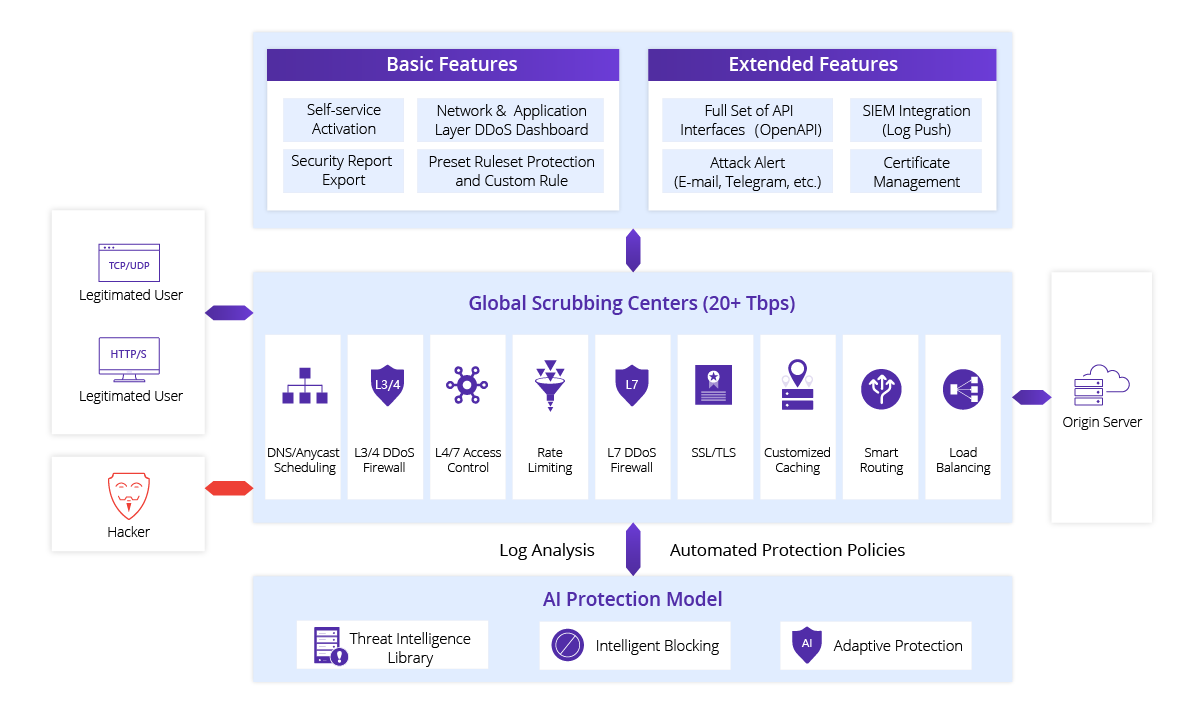
Flood Shield 2.0 is provided as a simple DNS change, typically to protect websites, TCP/UDP applications, and ports. With customer traffic routed through CDNetworks’ PoPs, attacks hit the CDNetworks infrastructure rather than customer servers and networks. CDNetworks’ PoPs detect and deflect both application-layer attacks (L7) and all known types of network-layer attacks (L3/L4).






